What Happens After BGP?
Gaining Full Path Visibility in Hybrid Cloud Networks In the modern enterprise, Border Gateway Protocol (BGP) plays a foundational role in connecting distributed networks. It is the routing protocol that...
Join us at NetBrain LIVE 2025 – Learn, Connect, Grow!
by Kelly Yue Nov 7, 2023
Network security is a critical exercise in continuous vigilance. Threats evolve and new vulnerabilities are discovered every day. Case in point, on October 16th, 2023, Cisco revealed the existence of previous unknown vulnerabilities, CVE-2023-20198 and CVE-2023-20273 (Cisco Bug ID: CSCwh87343), affecting all of Cisco’s IOS XE products. This exploit takes advantage of IOS XE’s web-UI functionality, regardless of whether it is configured for HTTPS or not. Per the Cisco website:
These vulnerabilities allows a remote, unauthenticated attacker to create an account on an affected system with privilege level 15 access. The attacker can then use that account to gain control of the affected system.
This bug was given a Common Vulnerability Scoring System (CVSS) score of TEN, the most critical and severe of vulnerabilities, which usually warrants taking immediate action to resolve.
The absolute quickest way to respond to any real-world network problem is with NetBrain’s no-code Network Intents: instant automation that every network engineer can apply without programming or coding.
Within minutes of receiving the Cisco security advisory, one of our customer support engineers had already begun plugging these security vulnerabilities for our customers using our no-code network automation. We knew time was of the essence and wanted to assist our customers to respond quickly within their own hybrid networks. Using the materials we supplied to all our customers on that first day, NetBrain power users were able to quickly create a set of Network Intents to identify the CVE-affected IOS XE devices across their entire network and allow their operators to repair each affected device.
Let’s briefly investigate how NetBrain’s Next-Gen platform helped our customers identify this timely example of where they were vulnerable and open to attack.
In the CVE advisory, Cisco recommended disabling both the HTTP and HTTPS servers with the “no ip http server” and “no ip http secure-server” commands, respectively. If your devices do have HTTP and HTTPS servers enabled, the following log messages are indicators your system may have been compromised.
%SYS-5-CONFIG_P: Configured programmatically by process SEP_webui_wsma_http from console as user on line %SEC_LOGIN-5-WEBLOGIN_SUCCESS: Login Success [user: user] [Source: source_IP_address] at 03:42:13 UTC Wed Oct 11 2023 %WEBUI-6-INSTALL_OPERATION_INFO: User: username, Install Operation: ADD filename
 Assessing For Network Vulnerabilities at Scale
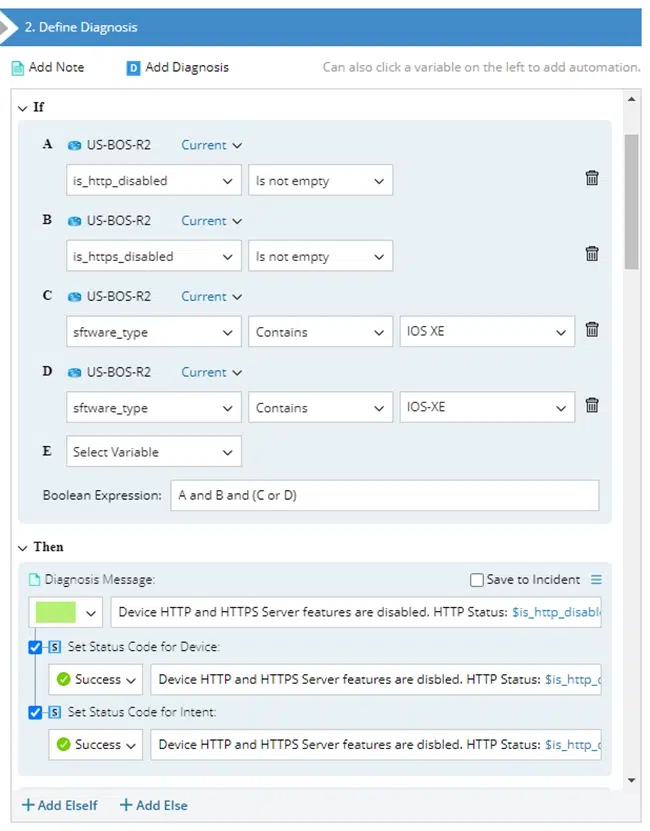
Assessing For Network Vulnerabilities at ScaleGiven the set of indicators provided by Cisco, NetBrain’s no-code interface allows us to create automation that mimics what an SME would do, but at scale. For these particular Cisco CVSS 10 vulnerabilities, we built a pair of Network Intent based assessments:
In no time at all, our clients were running the interactive network automation Intent to quickly detect and mitigate the pressing vulnerabilities.
If you look beyond this CVE problem and at the bigger opportunity, you’ll find there are a ton of operating conditions, firmware versions, traffic flows, access controls and failover capabilities that you should be checking all the time. Not to mention all the known root causes of your most common service desk tickets as well as your security policies and access control architecture.
With NetBrain Next-Gen and its Network Intent and Preventive Automation technologies, continuous network assessment can be done quite easily. Any condition or operating parameter that could be manually tested by your best SME, can be automatically and continuously tested by NetBrain… at scale!
NetBrain recommends scheduling Intents like the ones designed for this CVE continuously to prevent the same kind of vulnerabilities from reappearing in the future. Continuous network assessment is part of Next-Gen’s core capabilities and found in our Preventive Automation module. When a broad set of operating conditions are validated continuously, automated and continuous network assessment can become the cornerstone in your service delivery and outage prevention strategy.
No-code network automation scales your NetOps capacity in minutes, not months. As operational threats to network services continue to evolve, it’s crucial to maintain a proactive approach to NetOps- simply responding to the countless number of service incident reports each day is a highly ineffective and costly plan.
NetBrain Next-Gen was designed with that singular goal in mind, to leverage the knowledge found within your network experts to effectively scale their experience through no-code. It is enabled by our 4-layer Digital Twin, that provides every real-time detail about device, topology, traffic and desired behaviors as the foundation for no-code automation.
Although this Cisco bug example was a critical extreme, the same simple no-code approach can be repeated for any operating condition that must be verified or maintained. The steps to create no-code automation from scratch –without the need for software developers or programming of any kind—are the same:
Network operations is an ongoing process and no-code automation should be the ongoing foundation for that process. Your real-time business cannot afford to wait for, nor has the resources to address at scale, latent, hidden issues waiting to disrupt your services. Your network engineers must spring into action and play to their strengths as soon as new threats emerge. In doing so, protect your business, its network and reputation from potential harm.
Gaining Full Path Visibility in Hybrid Cloud Networks In the modern enterprise, Border Gateway Protocol (BGP) plays a foundational role in connecting distributed networks. It is the routing protocol that...
Your Network Automation Is Holding You Back Network teams across industries are caught in an automation paradox. While 64% of enterprises rely on homegrown scripts and open-source tools like Ansible,...
NetBrain CEO Insights from ISMG Interview at RSAC How Agentic AI decodes network intent to automate diagnosis In the rapidly evolving world of IT infrastructure, preventing recurring network outages...
We use cookies to personalize content and understand your use of the website in order to improve user experience. By using our website you consent to all cookies in accordance with our privacy policy.