Discovering Network Devices
The live network discovery function enables you to discover your network devices and provides a granular view of your network infrastructure.
Desired Outcome: All managed network devices are discovered.
The system provides the following two ways to discover your network.
▪Discovering Network via Seed Routers
▪Discovering Network by Scanning IP Range
Note: Before discovering your network devices, you need to make sure that the connections between NetBrain Front Servers and your live network are working, and all available credentials are configured in the Network Settings to access your devices.
Note: The time to finish the discovery process depends on your network scale. To narrow down the discovery scope, you can exclude devices by adding them to the Do-Not-Scan list.
Note: Network Definition is recommended as a workaround if SNMP is not accessible on specific devices temporarily when discovering a network. During the discovery, the system uses the settings in the Network Definition to discover a device when the SNMP of this device fails.
Note: After the discovery, the system will add the newly discovered devices to your domain and perform additional operations, including building Layer 3 topology, synchronizing with sites, and updating the CE devices of the BGP MPLS cloud.
Tip: You can view and select history result by clicking Select right beside View Historical Result. By default, it will show the discovery history in the past 30 days, and user can select which history to view.
Tip: You can select the API server from the Select API Servers window for the API discovery. See Discovering ACI Single Site in NetBrain Domain for more information.
Discovering Network via Seed Routers
A seed router is the starting point where the discovery begins. With the seed router method, all the discovered neighbor devices will be treated as new seeds, until all devices matching the defined Discovery Depths are discovered. The system enables you to discover all the neighbor devices from the route tables, NDP tables, and SNMP routing protocol neighbors.
1.Log in to the Domain Management page.
2.In the Domain Management page, click Discover on the Start Page or select Operations > Discover from the quick access toolbar.
3.On the Discover tab, the method Discover via Seed Routers is selected by default. Select one of the following ways to enter one or multiple seed routers:
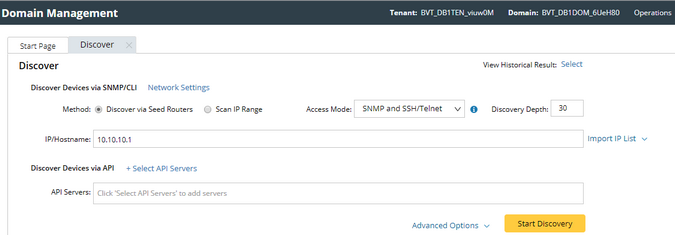
▪Enter seed IP addresses directly in the blank field, separated by semicolons. The live network discovery starts from these IP addresses.
▪If you already have any devices discovered in your domain, click Import IP List>Select Devices.
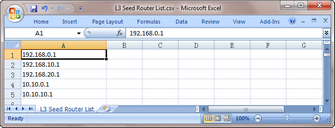
▪Import a .csv or a .txt file by clicking Import IP list. Here is a sample list for your reference:
4.Select one of the following options from the Access Mode drop-down list.
▪SNMP and Telnet — retrieve vendor and model information via SNMP first, and then log in to devices by using Telnet to retrieve live data.
▪SNMP and SSH — retrieve vendor and model information via SNMP first, and then log in to devices by using SSH to retrieve live data.
▪SNMP and Telnet/SSH — retrieve vendor and model information via SNMP first, and then log in to devices by using Telnet to retrieve live data; if Telnet doesn't work, then use SSH.
▪SNMP and SSH/Telnet — retrieve vendor and model information via SNMP first, and then log in to devices by using SSH to retrieve live data; if SSH doesn't work, then use Telnet.
▪SNMP Only — retrieve live data via SNMP only.
Note: The data retrieved via SNMP only might be incomplete.
5.Set the discovery depth by entering a value between 0 and 255.
It refers to how deep you want the discovery to go. That is, how many levels of neighbors are explored from the seed router (the neighbors can include NDP neighbors, routing protocol neighbors, and next-hops in route tables, which depend on your configurations). Here is a sample for discovery depth.

6.Click Advanced Options to configure more settings:
▪Run additional operations after discovery — choose to whether to run the additional operations for the discovery, including updating MPLS Cloud CE list, building IPv4 L3 topology, sites and so on. It is recommended to keep this option checked, otherwise the discovered devices will not be ready until the benchmark task finishes.
▪Retrieve device/module/interface information — choose to whether to retrieve the device/module/interface information for certain discovery (for example, AWS discovery to merge the multi-source devices and Juniper discovery for complete MIB information).
▪CLI Forced Timeout — the time limit of each CLI command to retrieve live data from a device. The default value is 600 seconds.
▪Use NDP to discover neighbor devices — discover neighbor devices by looking up an NDP table.
▪Find routing protocol neighbor via SNMP — retrieve routing protocol (such as BGP, EIGRP, and OSPF) neighbors via SNMP.
▪Use CLI routing table to discover next-hops — discover neighbor devices from route tables retrieved by CLI commands.
▪Scan destination subnets — continue to scan all destination subnets in the route tables of the devices that are discovered in the last depth.
Note: The option is only available when the Use CLI routing table to discover next-hops option is selected.
▪Scan all connected subnets — continue to scan all directly connected subnets of the devices that are discovered in the last depth.
oMinimum mask bits — scan subnets with mask exceeding the threshold. The default value is 24 and can be configured between 22 and 32.
7.To specify the proxies and credentials to be used in the discovery, click Network Settings to adjust.
8.Click Start Discovery.
9.When the discovery task is finished, the discovered devices are automatically added to the current domain.
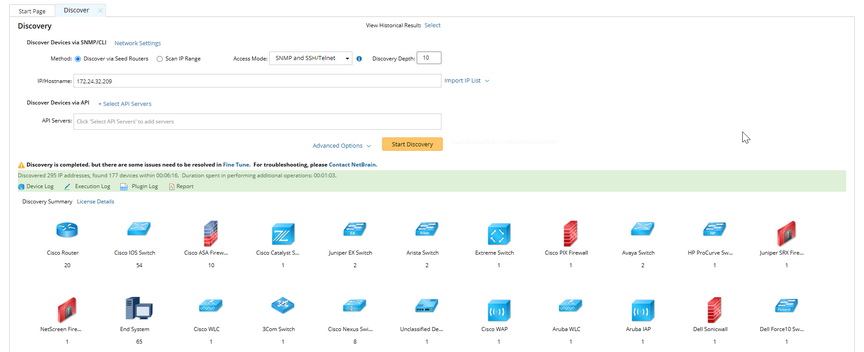
You can click Device Log to view the access log of discovered devices or click Execution Log to view the execution log of the entire discovery process.
Discovering Network by Scanning IP Range
The scanning method only discovers devices in the specified IP range or subnet. It is recommended to use this method to discover a large-scale network, which is divided into subnets and each of which occupies a range of IP addresses.
1.Log in to the Domain Management page.
2.Click Discover on the Start Page or select Operations > Discover from the quick access toolbar.
3.On the Discover tab, select Scan IP Range and use one of the following ways to specify the IP range:
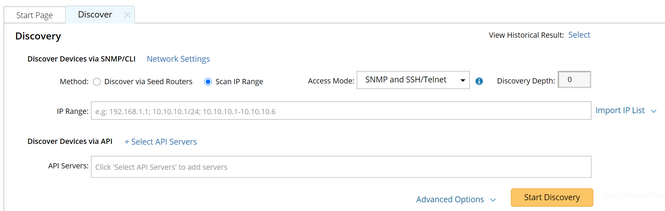
▪Enter an IP range directly in the blank field, separated by semicolons. For example, enter 192.168.2.1 as a single IP address; enter 10.10.10.1/24 as a segment address; enter 10.10.10.1-10.10.10.6 as an IP range.
Note: Under the premise of meeting the requirements, it is highly recommended to enter a segment address as small as enough to ensure a smooth discovery process.
▪Import a .csv or a .txt file by clicking Import IP List. Here is a sample list for your reference:
4.Select one of the following options from the drop-down list of the Access Mode field.
▪SNMP and Telnet — retrieve vendor and model information via SNMP first, and then log in to devices by using Telnet to retrieve live data.
▪SNMP and SSH — retrieve vendor and model information via SNMP first, and then log in to devices by using SSH to retrieve live data.
▪SNMP and Telnet/SSH — retrieve vendor and model information via SNMP first, and then log in to devices by using Telnet to retrieve live data; if Telnet doesn't work, then use SSH.
▪SNMP and SSH/Telnet — retrieve vendor and model information via SNMP first, and then log in to devices by using SSH to retrieve live data; if SSH doesn't work, then use Telnet.
▪SNMP Only — retrieve live data via SNMP only.
Note: The data retrieved via SNMP only might be incomplete.
5.To specify the proxies and credentials to be used in the discovery, click Network Settings to adjust.
6.Click Start Discovery.
7.When the discovery task is finished, the discovered devices are automatically added to the current domain.
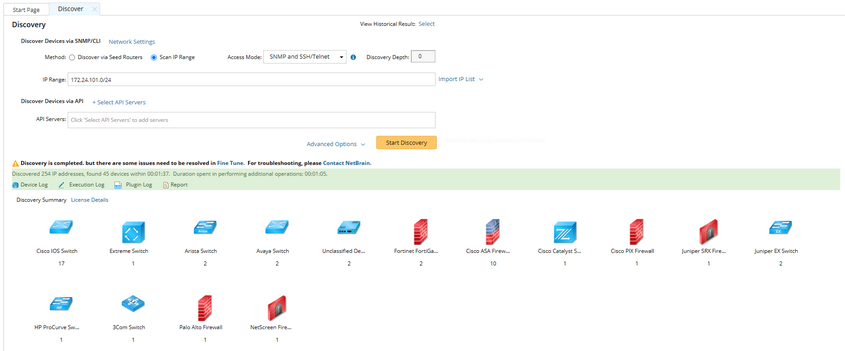
You can click Device Log to view the access log of discovered devices or click Execution Log to view the execution log of the entire discovery process.
See also:
