Configuring SSO Authentication
1.Log in to the System Management page.
2.In the System Management page, click User Accounts > External Authentication.
3.Click the ![]() icon and select Add SSO Authentication from the drop-down list.
icon and select Add SSO Authentication from the drop-down list.

1)Enter a unique name to identify the SSO server and a brief description.
2)Enter the credentials to connect to the SSO server. See SSO Settings for more details.
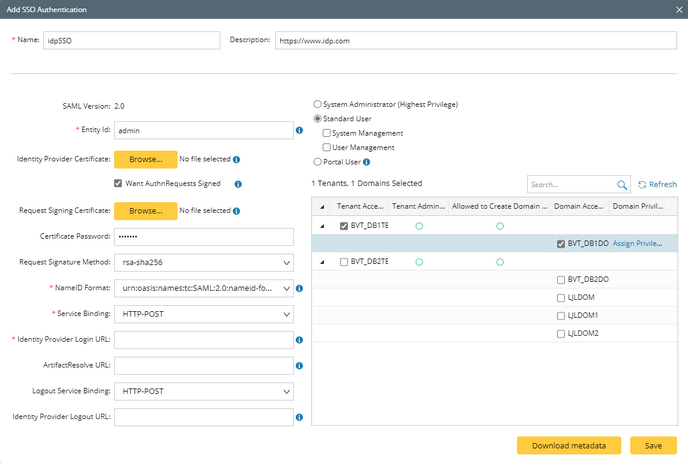
3)Assign the access permissions, roles and privileges to the user accounts on the SSO server.
▪System Admin — click to assign the system administrator role to the user accounts. For the detailed privileges of System Management and User Management, refer to Featured Management Privileges.
▪Tenant Access — select one or more tenants to assign access permissions to the user accounts.
▪Tenant Admin — select one or more tenants to assign the tenant administrator role to the user accounts.
▪Allowed to Create Domain — select the check box to assign the domain creation permission to the user accounts.
▪Domain Access — select one or more domains to assign access permissions to the user accounts.
▪Domain Privileges — click Assign Privileges to assign more domain privileges to the user accounts by role. See Share Policy for more details.
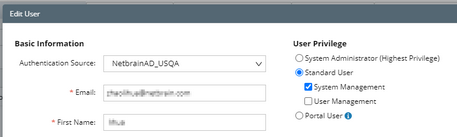
Note: To prevent the assigned roles and privileges of an external user account from being synced with any changed authentication settings, you can lock the user rights as follows as soon as the user has logged in to the IE system. See Creating User Account for more details.
4)Click Save.
Tip: You can click Download metadata to download the SAML metadata of NetBrain Service Provider, which contains entityID, endpoints (Attribute Consume Service Endpoint, Single Logout Service Endpoint), public X.509 certificate, nameID format, organization information, and so on.
SSO Server Settings
The following table lists the credentials that are required when connecting to an SSO server.
Note: To ensure the X.509 certificates can be deployed on IIS, go to IIS Manager > Application Pool > Advanced Settings > Process Model and set Load User Profile to True.
Field |
Description |
|---|---|
SAML Version |
The version of SAML used by your Identity Provider. Currently, SAML 2.0 is supported. |
Entity Id |
The unique identifier of the Identity Provider. |
Identity Provider Certificate |
The X.509 certificate containing the public key to verify the SAML 2.0 messages signed by the Identity Provider, such as the Assertion and LogoutRequest/LogoutResponse. Click Browse to upload the certificate. Note: Only the .crt format is allowed. |
Request Signing Certificate |
The X.509 certificate containing the public key and private key to sign outgoing SAML 2.0 messages and decrypt incoming SAML 2.0 messages encrypted by the Identity Provider, such as the Assertion/NameID/Attribute elements inside an SSO Response. The certificate with password is supported. Click Browse to upload the certificate. Note: Only the .pfx format is allowed. |
Certificate Password |
The password of the certificate (pfx). |
Want AuthnRequests Signed |
Set whether to sign the SAML authentication request with NetBrain certificate. Note: Select the check box if your Identify Provider enables the certificate signature for received messages through the security settings. |
Request Signature Method |
The signing algorithm to encrypt the messages sent to the Identity Provider. The available options include: ▪rsa-sha1 ▪rsa-sha256 ▪rsa-sha384 ▪rsa-sha512 |
NameID Format |
The name identifier formats supported by the Identity Provider. Name identifiers are a way for providers to communicate with each other regarding a user. SSO interactions support the following types of identifiers: ▪urn:oasis:names:tc:SAML:2.0:nameid-format:persistent ▪urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified ▪urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress |
Service Binding |
The binding used to send the login request to the Identity Provider. The available options include: ▪HTTP-Redirect ▪HTTP-POST |
Identity Provider Login URL |
The Login Service URL where the Identity Provider will redirect the user during the login exchange. |
ArtifactResolve URL |
The Artifact Resolution Service (ARS) URL to send back-channel requests to resolve artifacts received from NetBrain. |
Logout Service Binding |
The binding used to send the logout request to the Identity Provider. The available options include: ▪HTTP-Redirect ▪HTTP-POST |
Identity Provider Logout URL |
The Logout Service URL where the identity Provider will redirect the user during the Logout exchange. |
