Your production hybrid network sees hundreds or thousands of service tickets per month, all rooted in network-based applications. Network Operations teams often start working on these tickets by attempting to gather documentation of the problem areas. The challenge is that written documentation is scarce, incomplete, inaccurate, and out of date. And, even in best-case scenarios, networking documents typically focus on physical connectivity instead of logical connectivity and performance.
NetBrain network documentation software understands every aspect of your hybrid network and then renders a data model in real-time. NetBrain uses this model to generate real-time dynamic maps of your network, which become the foundation for network automation.
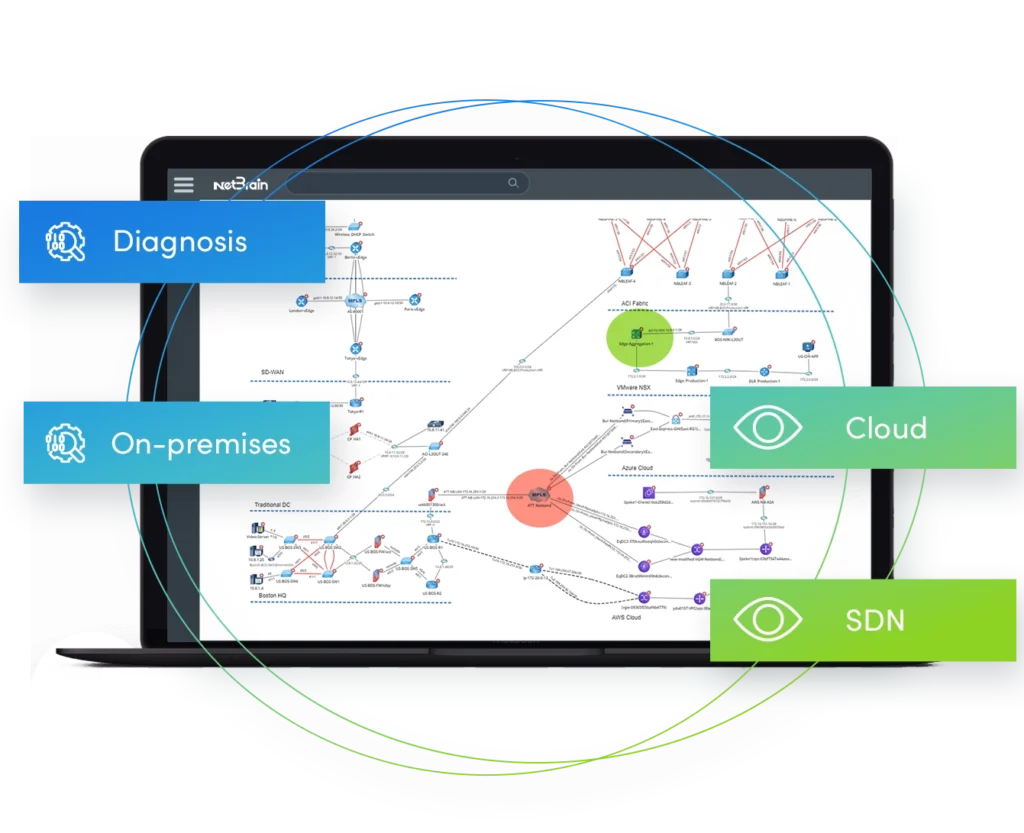
Mapping your Hybrid Network in Real-Time
NetBrain uses a mathematical model generated by a powerful discovery engine to generate a live “digital twin” of your network. It collects and aggregates data from complex physical and logical topologies across geographically distributed sites, including software-defined LAN and WAN deployments, and presence in any major public cloud. It visualizes any part of your network in real time and identifies performance issues, STP status, multicast or QoS policies, firewall rules, and more.

Highly-Informed Problem Solving
NetBrain leverages all of the available data from its robust and continuously updated digital twin, which includes historical baselines as well as real-time analytics from third-party monitoring applications, to help solve issues and tackle problems with the utmost efficiency. API support enables the diagnosis of SDN and cloud networks with a single pane of glass using Data View Templates from an external system such as Splunk, SolarWinds, and ServiceNow. Intent Data Views add color-coded diagnostic information directly onto any map or path for easy troubleshooting with the relevant connectivity details and context so you can solve problems faster.
Improving Agility through Collaboration
NetBrain’s Incident Management Dashboard provides real-time messaging and central problem visualization for easy collaboration. By enabling diverse operational teams to work together on service tickets in real-time, problems can be resolved more quickly. And without the typical hand-offs and escalation processes when multiple groups are involved, MTTR times are reduced.
