by Mark Harris Apr 3, 2019
by Mark Harris Apr 3, 2019
Organizations across the globe — whether government, public, or private — are often challenged by the increasing pace, complexity, and sophistication of cyber-attacks. A recent PricewaterhouseCoopers report found that only 35% of business leaders are “very comfortable” that their company has adequately tested either its resistance to cyber-attacks or its cyber-incident response plan.
The PwC study of hundreds of incidents involving security and operational failures identified the common root cause in most cases as the “dependence on a highly siloed and reactive approach” to security.
A recent PricewaterhouseCoopers study found the common root cause of most cyber-incidents is a ‘highly siloed and reactive approach’ to security.
The report continued, “Businesses cannot count on an inconsistent web of solutions, policies, and procedures in a crisis, certainly not when attacks are becoming more sophisticated and the window for the right response is getting shorter.”
 However, your company’s network is not helpless against network threats. In fact, cyber-defense can be improved by proactively identifying what systems and networks are critical to the business’ complete infrastructure visibility (i.e., network, end points, events and secure configuration of the network infrastructure).
However, your company’s network is not helpless against network threats. In fact, cyber-defense can be improved by proactively identifying what systems and networks are critical to the business’ complete infrastructure visibility (i.e., network, end points, events and secure configuration of the network infrastructure).
To help frame the problem, both NIST and SANS endorse the Cyber Defense Workflow, which includes several steps to ensure your company is prepared for a cyber-attack: Identify & protect, detect & respond, and recover.
Identifying an attack before it happens
The first step to protecting your network from attacks is to identify vulnerabilities before they can be exploited. Thus, network engineers must document existing network infrastructure, including inventory and network maps, ensuring they’re able to pinpoint any issues that may arise. An engineer’s limited understanding of application requirements and traffic flows could be the downfall of a team’s ability to protect its network. A lack of understanding of existing design (security, routing, layer-2, etc.) will put teams a step behind a hacker during an attack.
Unfortunately, most teams live without accurate network diagrams because it can take months to document a large network, and once the project is complete, the maps are already out of date. NetBrain creates network mapping automatically and keeps them up-to-date.
How to respond to an attack
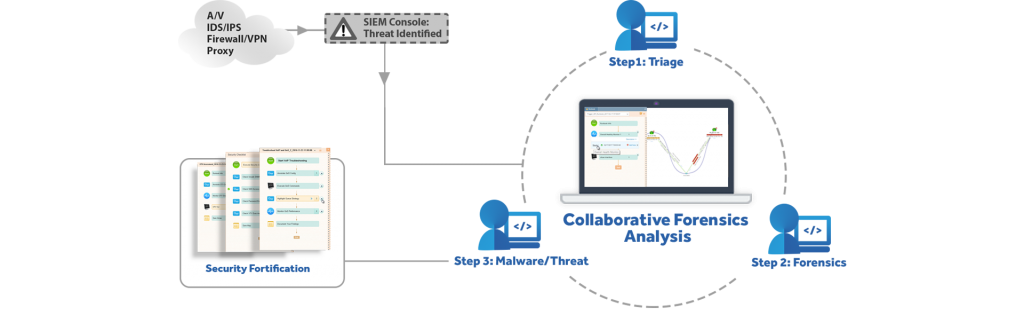
Network security is a cat-and-mouse game, and it’s virtually impossible to prevent every attack. When (not if) your network does fall victim, it’s important that network and security teams can identify and a respond promptly. It is very challenging to detect, analyze, isolate, and remediate a cyber-event. While network and security teams don’t typically collaborate, when a network is under attack, collaboration is instrumental to stopping the threat at hand. Dynamic Maps enable security and network teams work from a shared analytics console, to ensure that they’re both on the same page.
It is difficult to understand the live performance of the network (traffic flows, bandwidth utilization, interface errors, etc.). Teams need to ensure that all ingress/egress points from the internal networks to external networks are continuously monitored. NetBrain’s platform allows engineers to apply automation to every phase of network troubleshooting and acts as a single pane of glass — from ticket creation, to data collection, and for sharing knowledge of best practices.
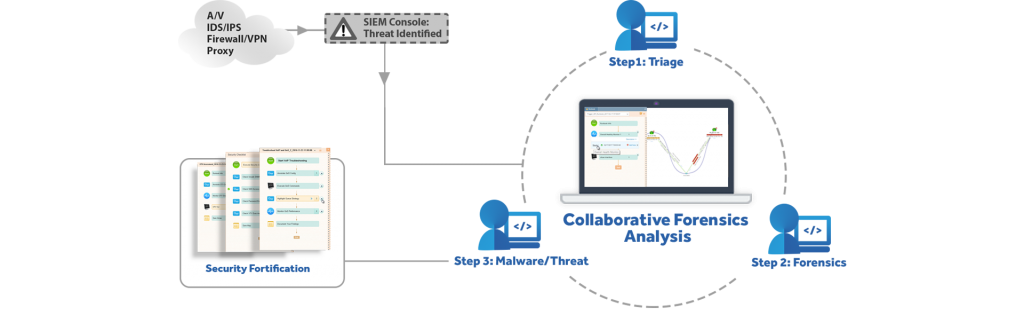
NetBrain can provide meaningful data around a potential cyber-incident via the API, and a diagnosis can be triggered that would create both a Dynamic Map and Runbook Automation the second an attack is detected. Further, NetBrain stores historical data that can be visualized to support forensic analysis, as the diagnosis of a cyber-event can often occur after the fact.
Recovery
Once a cyber-attack has been mitigated, network teams must update existing playbooks, incident response plans, and network infrastructure immediately.
Network and security teams can update the Runbook Automation that verifies and validates that the network is configured per industry standard compliance (e.g. NITS, PCI, HIPAA) and internal security requirements.
Regarding cyber-defense and incident response plans, it is best practice to use playbooks and rehearse regularly. With NetBrain, those can be automated, edited, and kept up to date via our Runbook Automation. NetBrain can provide the Adaptive Network Automation solution, which can help in mitigating ever-changing cyber threats.
Combat Cyber-attacks with Automation
Whether your team is prepared for a cyber-attack or not, NetBrain’s dynamic mapping and visual troubleshooting can help your network team uncover many network vulnerabilities. Collaboration between network and security teams prior to an attack, documenting your network’s infrastructure, and ensuring your team has a set plan in place will help your network become less susceptible to cyber-threats.
 However, your company’s network is not helpless against network threats. In fact, cyber-defense can be improved by proactively identifying what systems and networks are critical to the business’ complete infrastructure visibility (i.e., network, end points, events and secure configuration of the network infrastructure).
However, your company’s network is not helpless against network threats. In fact, cyber-defense can be improved by proactively identifying what systems and networks are critical to the business’ complete infrastructure visibility (i.e., network, end points, events and secure configuration of the network infrastructure).